With BYOD assuming its role as an industry standard, enterprises are now facing new challenges on how to manage their wireless networks. Smartphones and tablets have become a potential source for security breaches, while bandwidth-hungry applications such as HD video conferencing increasingly threaten overall network stability and performance. Edgecore Wi-Fi solution for enterprises provides a secure and reliable wireless network by combining standards-based 802.1X with detailed access control by user and location. With just one set of equipment, network administrators are able to virtually segment the network between employees and visitors. Additionally, user firewall policies can be defined to limit network access, while rogue AP detection aids in the discovery of unauthorized Wi-Fi devices that may compromise the corporate network.
FEATURES & BENEFITS
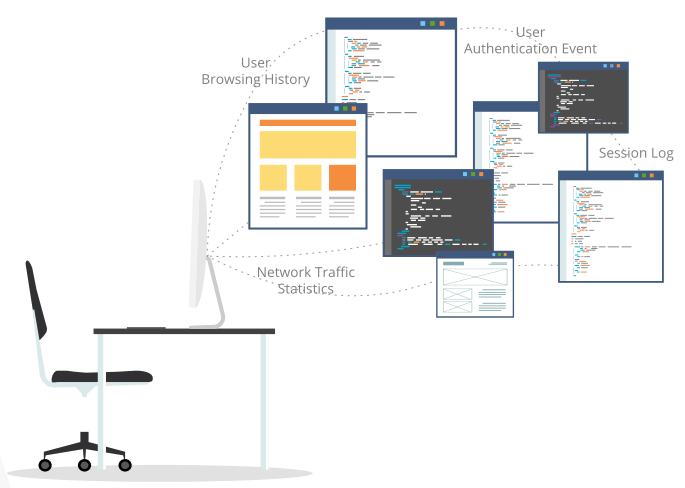
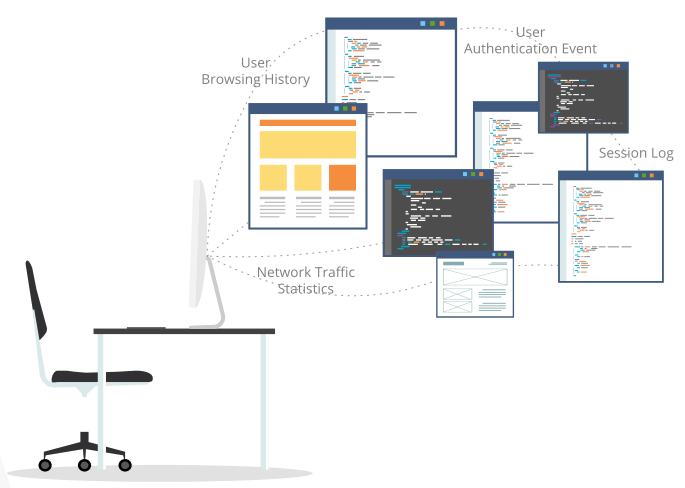
DETAILED USER LOGS & REPORTS
With increasing security regulations in both public and enterprise Wi-Fi deployments, WLAN solutions need to be able to effectively track all network activity. Edgecore offers a complete set of logs & reports from its monitoring interface, including user browsing histories, NAT conversion logs, and all authentication related events. Furthermore, the guest Wi-Fi platform allows administrators to aggregate unique user information such as social media profiles, cellular numbers, or e-mail addresses for detailed analytics or troubleshooting.
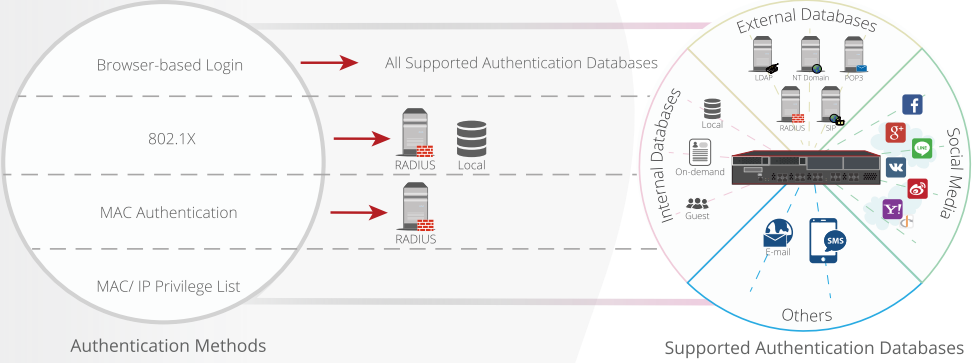
 SECURE ENTERPRISE USER AUTHENTICATION
SECURE ENTERPRISE USER AUTHENTICATION
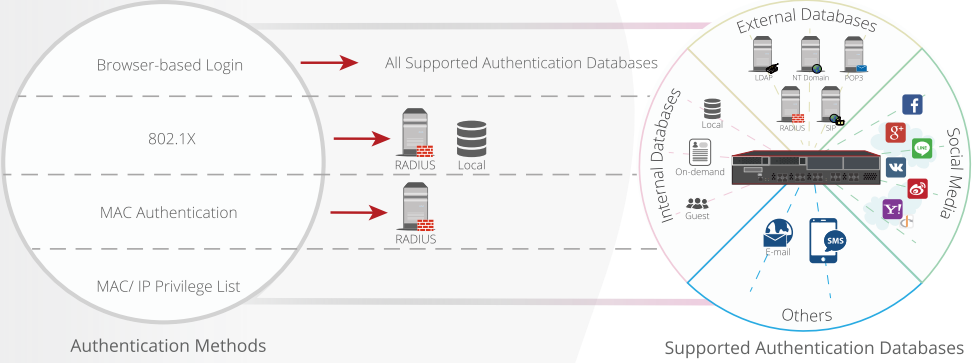
With the increase of BYOD devices such as smart phones and tablets accessing the company network, Wi-Fi access control is no longer optional. Enterprises need to have complete visibility of all users on their network as to prevent, identify, and fend off potential intruders. Therefore, Edgecore’s WLAN solutions support both browser-based and 802.1X authentication mechanisms to ensure the proper identification of network users before accessing the network. Network administrators can easily configure customizable captive portals for web-based authentication of employees. Alternatively, network administrators can configure authentication using external databases that are already present in the enterprise network, such as LDAP, POP3, NT Domain, and RADIUS. Either way, only network users with the proper credentials can access the company network.
802.1X WITH LOCATION-BASED ACCESS CONTROL

With Edgecore’s Service Zone functionality, enterprises can virtually segregate wireless network access
depending on the physical location of access points. For example, certain areas of the office can be
configured for restricted access to employees only, while public areas or lobbies can be open access to both employees and visitors. Furthermore, each Service Zone can have a unique configuration of enabled
authentication databases, access schedules, user policies, and independent network administrators.
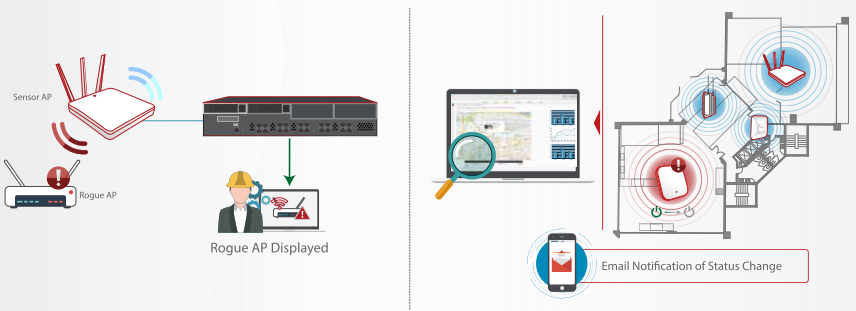
DETECTING UNAUTHORIZED ACCESS POINTS
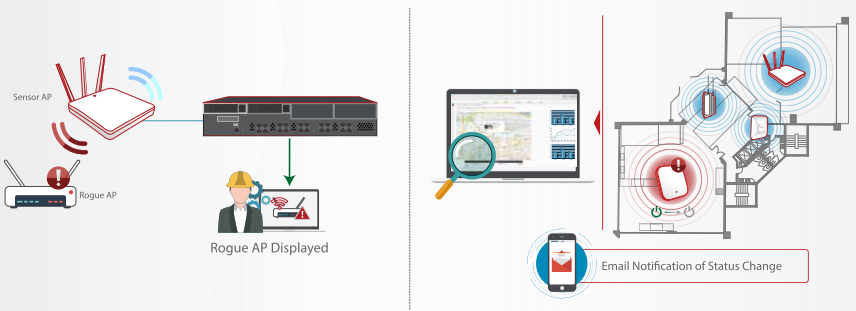
Rogue access points are often one of the primary sources of security beaches in an enterprise Wi-Fi network. They can potentially cause severe wireless interference, leading to network downtime and lost productivity. Edgecore's solution provides IT administrators with tools to easily monitor and detect rogue access points, allowing them to take swift responsive actions. Furthermore, network logs can show detailed information such as the access points that users authenticate from. Combined with detailed user events and browsing histories, Edgecore provides enterprises with full control over the security of their wireless networks.
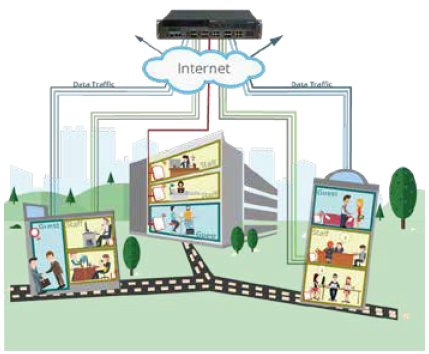
UNIFIED BRANCH OFFICE NETWORK POLICIES
Edgecore's solution supports both centralized and distributed access point deployments through flexible tunnel configuration between Edgecore APs and Integrated Wi-Fi products. For many enterprises, one of the key requirements is often to enforce unified policies across the entire corporation’s headquarters and branch offices. By configuring the access points to completely tunnel traffic back to the Integrated Wi-Fi products in the headquarters, network administrators ensure the same set of user policies and network resource access regardless of geographical location. As the tunneling is configured on a per SSID level, organizations can also choose to allow only employee traffic to return back to the HQ, while guest and visitor traffic can locally break out to the Internet.
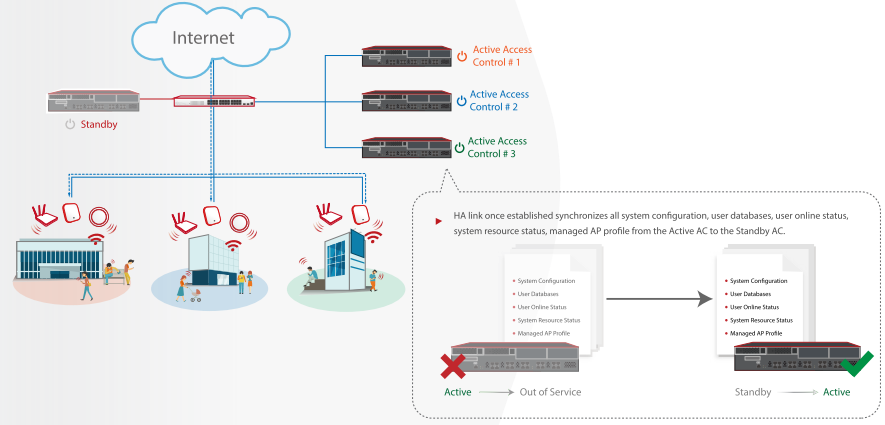
 ROBUST DESIGN WITH HIGH AVAILABILITY
ROBUST DESIGN WITH HIGH AVAILABILITY
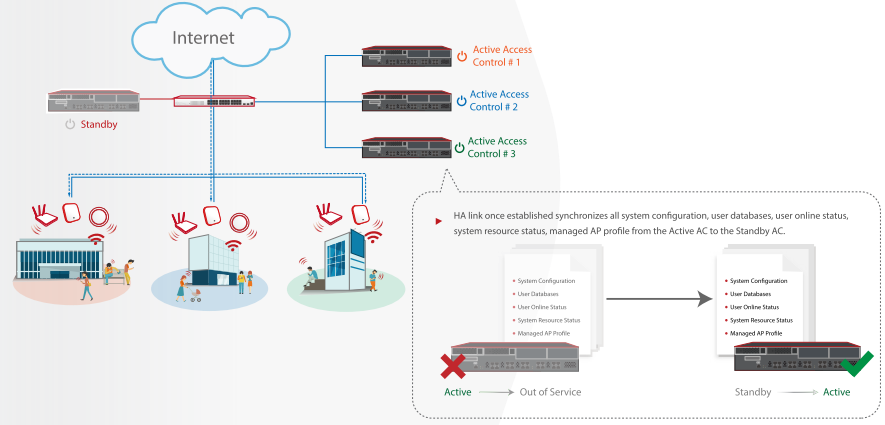
As Wi-Fi becomes the primary form of connectivity for many enterprises and organizations, a robust and reliable WLAN solution is of the utmost importance. To guarantee reliable WAN connectivity, Edgecore's Integrated Wi-Fi products can be attached to two WAN links from separate ISPs for redundancy and load balancing purposes. Furthermore, the entire system can be deployed in High Availability, mitigating the potential lost productivity in the event of network downtime. And with the ability to configure backup AP management controllers for remotely managed APs, network administrators can guarantee seamless network operation and management.
Wireless Product
Controller-based WiFi Aps
ECW5211-L Wireless Indoor AP - concurrent dual-band 802.11ac Wave 2 indoor access point
ECW5210-L Wireless Indoor AP - concurrent dual-band 802.11ac indoor access point
Wireless Controller
EWS5204 Enterprise-grade wireless LAN controller, managing up to 600 wireless access points